For a long time I've felt that the usefulness of antivirus has been declining and I'm starting to wonder when it will finally die out, or more likely be absorbed into other security products and cease to exist as a standalone product.
Looking at enterprise (and completely ignoring home users for the moment) I think antivirus has past it's prime and is effectivly useless. Black listing software with a list of signatures1 of known bad software simply doesn't scale. When I read through Metasploit - The Penetration Tester's Guide Chapter 7: Avoiding Detection coverd the use of packers such as UPX.
Packers are tools that compress an executable and combine it with decompression code. When this new executable is run, the decompression code re-creates the original executable from the compressed code before executing it. This usually happens transparently so the compressed executable can be used in exactly the same way as the original. The result of the packing process is a smaller executable that retains all the functionality of the original. As with msfencode, packers change the structure of an executable. However, unlike the msfencode encoding process, which often increases the size of an executable, a carefully chosen packer will use various algorithms to both compress and encrypt an executable. Next, we use the popular UPX packer with Back|Track to compress and encode our payload3.exe payload in attempt to evade antivirus software detection.
UPX was first release in 1998 and repacking software to avoid anitvirus detection has become even more mainstream now. In 2009 Brian Krebs wrote a great article about virus scanners for virus authors, sites where you can submit your files and check to make sure they don't get detected by any antivirus products.
Malware like CryptoLocker is packaged before it's sent out in spam emails. Often in addition to packaging it's also either zipped with a password that's provided in the body of the email or it's a link with to a page with a captcha to defeat email scanning from picking it up. I was at a security forum recently and people were discussing their experiences with CryptoLocker2 and everyone said that their fully patched and up to date desktop antiviurs (from a wide variety of vendors) had missed it, but that within 24 to 48 hours had signatures.
24 hours to add signatures is incredibly fast, but clearly it's not fast enough. Updating signatures can never be fast enough, conceivably malware authors could uniquely package every single file they send out.
Within an enterprise there are much better ways to deal with malware. I believe application whitelisting, patching software and reducing user permissions is far more effective than antivirus can ever be. Antivirus has been bumped down the chain of the ASD top 35 to number 22. With the top 4 being Application whitelisting, Patch applications, Patch operating system vulnerabilities and Restrict administrative privileges.
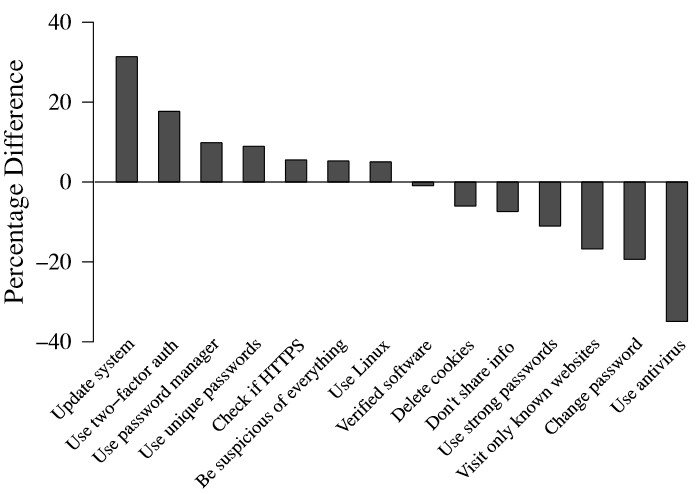
There was a great paper Comparing Expert and Non-Expert Security Practices which showed that the top thing security experts did to stay safe was update their system while the top thing non-experts did was run antivirus.
I don't know any Linux or Mac users that run antivirus and I know a few Windows users who don't run antivirus (they also don't run Java, Flash Player, Silverlight or other browser plugins and they keep their systems up to date.)
Maybe in a home environment where the users need administrative access3 to install new programs and updates, where whitelisting and removing privileges is not an option something like antivirus to say "Are you sure you want to run trojan.exe?" might still be useful. But in the enterprise I think its days are numbered.
-
This includes antivirs that uses heuristics ↩
-
Fortunately everyones experience could be summed up more or less as "reimage the desktop, restore any encrypted files on network shares from the backups, get on with your day" ↩
-
They don't need to run as an administrator but they need access to do things as administrator, I don't run as root but I have sudo. ↩
