I read Liars & Outliers in September 2012 however I've only just decided to review it now in September 2015 so this review could be seen as "Which points had enough impact that they stuck with me for 3 years?". There might be some mistakes in this review from my hazy memory but I've got my copy with me to thumb through so I should be able to check it.
It was the first of Bruce Schneier's books that I'd read and one of the things that struck me about his writing style was the number of references and foot notes he made1. Of the 368 pages in the book 250 are the main content and the other 118 are references and foot notes. You are left with the impression that Bruce is not just imparting his views of the world, but has solid well researched scientific evidence to back them up.
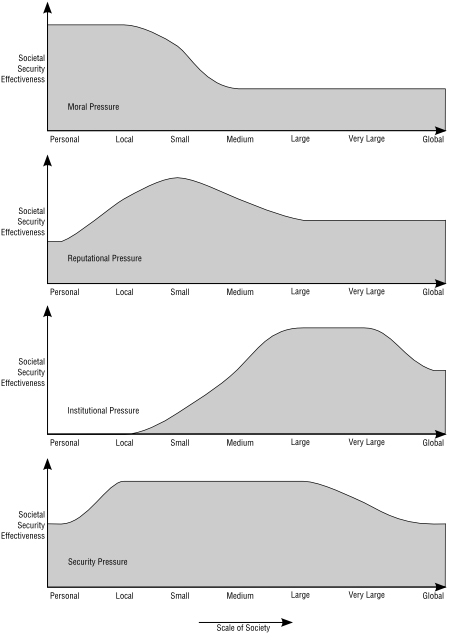
It centres around the question of how we have managed to achieve trust in our society and focus on the idea of four key "societal pressures" that we impose on people to create trust.
- Moral Pressures - Ethics, Doing the right thing because it's right, generally more of an individual thing but can be applied to organisations too.
- Reputational Pressures - If people know you are a crook they won't work with you, if your organisation has a reputation for not honoring warranties people won't buy your products.
- Institutional Pressures - Laws, taxes, regulations these scale up very well but are harder to enforce on an individual level.
- Security Systems - What most people think about as more traditional security, things like firewalls and padlocks. Designed to prevent people from being able to do the wrong thing even if they want to.
I think this graph taken from page 71 neatly sums up how different societal pressures scale from small communities of just a few people to global communities.
I think it's very useful for security professionals (and executives) to understand that "Security Systems" is not the only way to prevent unwanted behavior, and often not the most effective.
A classic example of when another type of pressure is more appropriate and often more effective is web filtering. I've seen schools that have a proxy serve scanning all images3 running some sort of image recognition technology over them trying to find and block pornographic content. Needless to say it didn't work well, with photos of Patric Stewart tripping the sensors because they had "too much smooth skin tone".
Another area that it comes up that we really don't like to talk about as systems administrators is ensuring that people with root access do the right thing. While it is possible to design a system such that even the systems administrators don't have access to sensitive content it's incredibly hard4. I most organisations the administrator have unrestricted and uncheked assess. They are not restricted by the fourth pressure "Security Systems" but most sysadmins still do the right thing because of Moral, Reputational and Institutional pressure.
That is not to say that we shouldn't try to design systems that force the administrators to to the right thing but that it's naive to think that people are only doing the right thing because security systems force them to.
Imagen saying to an auditor "Well, most sysadmins could snoop on employee email but they don't because it's morally wrong, and they know that if they got caught they might lose their job or face legal issue but they would definitely lose the respect of their colleagues" it doesn't sound very good but for many organistions it's true, and for many organisations it's enough of a deterrent.
While saying something like "We log all access to email and check it on a monthly basis and require two admins to authenticate before giving access to another users account." now that sounds great! If you can achieve a system like that brilliant, but it doesn't often work out like that in reality.
I think it's wise to pay attention to these situations and know where you are not protected by a security system. Have a think about your organisation and where people have access but are using it responsibly.
-
Maybe this struck a cord with me because I like foot notes2. ↩
-
I mean I like them so much I recursively put foot notes in my foot notes about how much I like foot notes. ↩
-
And breaking HTTPS in the process by putting a local CA cert onto all the computers and Man-in-the-Middleing the connection. ↩
-
As we have seen from the Snowden and Manning leaks even the NSA / Army struggles with this. Snowdn and Manning had access to thousands of sensitive documents and were able to hoover them up without tripping alarms. ↩
